Werner Vermaak
Web3 Content Strategist
Werner Vermaak is a Web3 author and crypto journalist with a strong interest in cybersecurity, DeFi, and emerging blockchain infrastructure. With more than eight years of industry experience creating over 1000 educational articles for leading Web3 teams, he produces clear, accurate, and actionable organic material for crypto users.
Learn
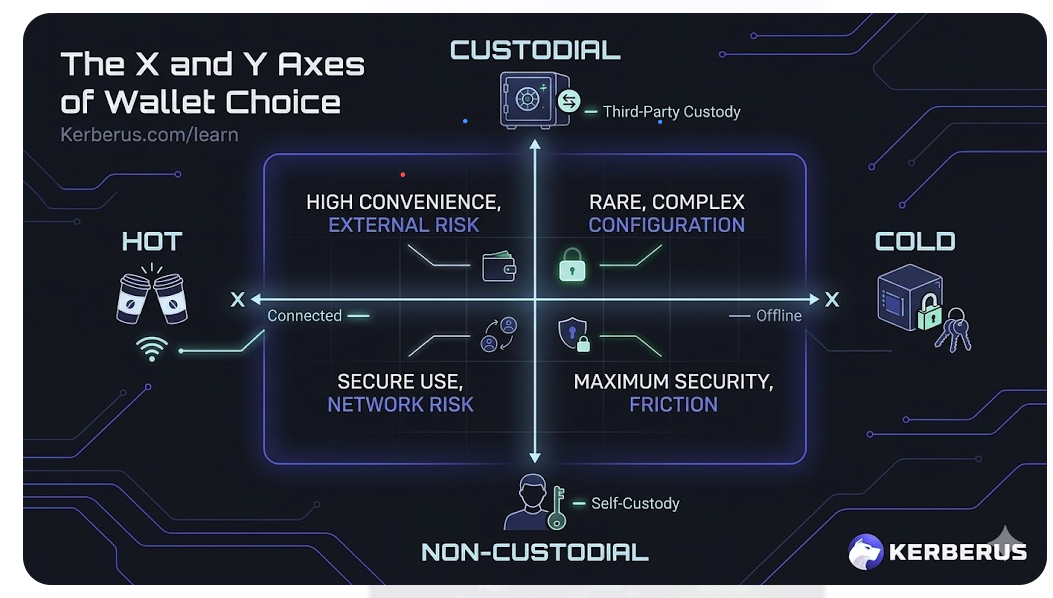
Crypto Wallets For Beginners: Your Need-To-Know Guide
Hot or cold, custodial or self-custody, the wallet you pick determines how safe your crypto actually is. Here's how to make the right call in 2026.

Fake Airdrop Scams: Types and Red Flags To Avoid
Fake airdrops are one of the fastest-growing attack vectors in crypto. Here's how to claim real ones without getting your wallet drained.

How to Revoke Crypto Token Approvals in 2026
Step-by-step guide to revoking token approvals on Ethereum and Solana. Protect your wallet from dormant permissions that hackers exploit.

How to Read a Crypto Transaction Before You Sign It
Learn how to read crypto transactions, understand wallet prompts, and spot red flags before signing. Beginner guide with Etherscan walkthrough.
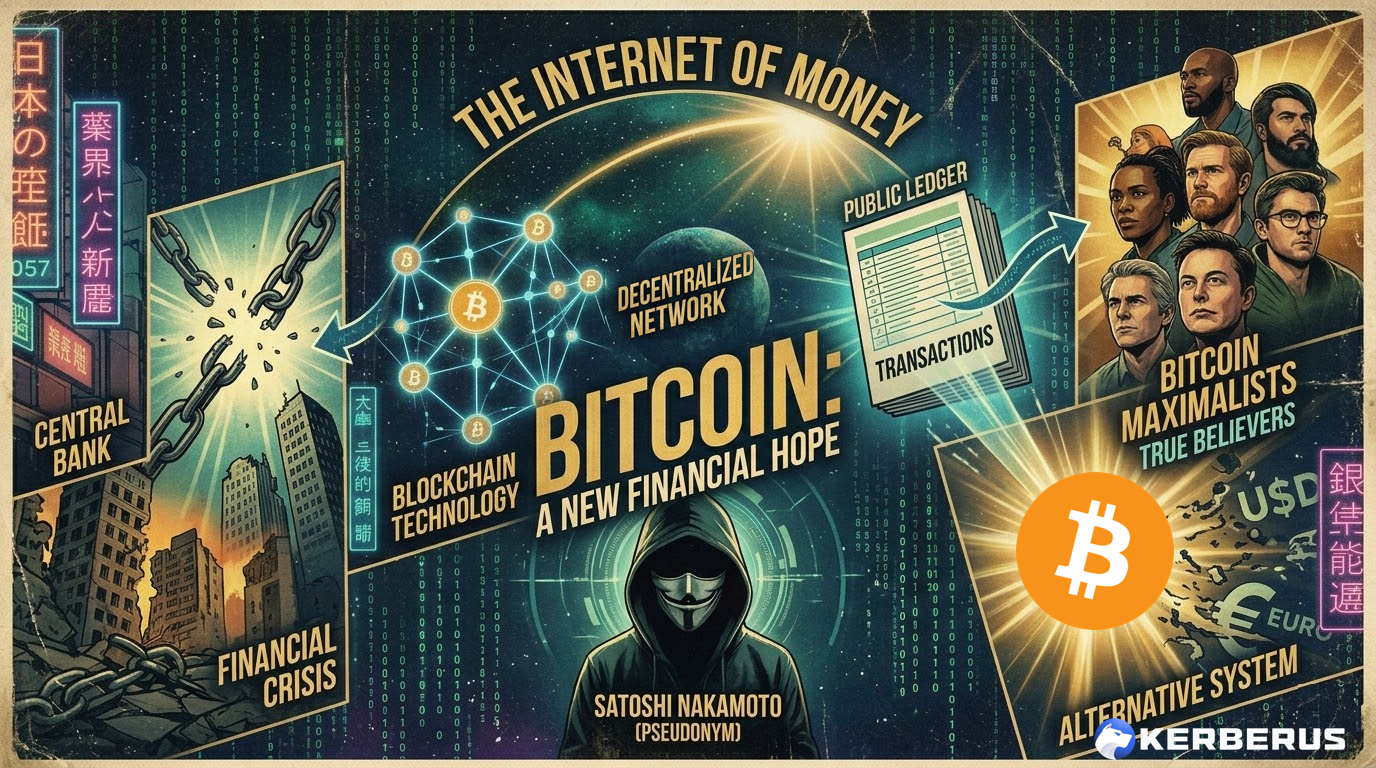
Bitcoin 101 For Beginners: BTC’s Past, Present and Future
A beginner's guide to Bitcoin covering its history, how it works, how to buy and store it securely, and where BTC is headed in 2026 and beyond.

Wallet Hygiene Guide: How To Keep Your Crypto Safe
Learn the most vital Web3 wallet hygiene practices to protect your crypto in 2026. Covers seed phrase security, wallet segregation, phishing prevention, smart contract approvals, and estate planning.

Solana 101: A 2026 Guide to SOL and Its Ecosystem
The complete Solana guide for 2026. Covers how SOL works, Firedancer, DeFi, staking yields, DePIN, institutional adoption, and how to keep your Solana assets safe.

Crypto and Web3's 12 Biggest Q2 Narratives in 2026
From prediction markets and ZK privacy to RWAs, DePAI, and agentic finance—discover the top crypto narratives driving Web3 in 2026 and where smart money is flowing.
![Honeypot Crypto Scam: How to Detect & Avoid Them [2026 Guide]](/images/blog/Blog_Default_Banner.png)
Honeypot Crypto Scams: How to Detect and Avoid Them
Honeypot crypto scams trap your funds in tokens you can't sell. Learn how honeypot smart contracts work, the latest scam variants in 2026, and the best tools to detect them before you invest.

How to Use Phantom Wallet Safely: A Beginner’s Guide
A comprehensive guide on how to use Phantom wallet safely, covering setup, transactions, staking, and essential security best practices.

Wake Up! WEF 2026 Cybersecurity Report Sounds Alarm For Crypto Sector
The World Economic Forum's Global Cybersecurity Outlook 2026 puts crypto in the crosshairs. AI threats, fraud, supply chain risks—here's what actually works.

What is Self-Custody in Crypto? A Complete Beginner's Guide
Learn what self-custody means, why it matters, and how to secure your crypto with real-time protection. Your keys, your coins.

Pig Butchering Romance Scams: How to Protect Your Crypto
Pig butchering scams stole $75B+ and grew 40% YoY. Learn how romance scammers use crypto to steal funds and how to protect yourself in 2026.

The Psychology of Crypto Scams: How And Why They Still Work
Learn how crypto scammers exploit human psychology to steal funds. Understand why even experienced users fall for scams and how to protect yourself from social engineering attacks.

Top 26 Web3 Security Threats In 2026
Comprehensive guide to all 26 Web3 security threats in 2026. Learn about social engineering, phishing attacks, private key compromise, malicious smart contracts, wallet drainers, DeFi exploits, and how to protect yourself from these critical risks.

The Ultimate Web3 Security Beginner Guide For 2026
Complete beginner's guide to Web3 security in 2026. Learn the 10 biggest risks, 3-layer protection strategy, and essential security practices to protect your crypto assets.

Address Poisoning Attacks: How They Scam Web3 Users
Learn how address poisoning attacks work, how to detect them, and protect yourself from losing crypto to lookalike wallet addresses. Complete guide with real case studies.

Kerberus CEO: "Web3 Users Shouldn't Be Getting Drained in 2025"
Alex Katz on fighting a culture that normalized scams, building real-time defense systems, and why Kerberus maintains zero user losses while protecting 250,000+ users.

Web3 Security Tools: How to Protect Your Assets in 2026
Comprehensive guide to the best Web3 security tools for 2026. Learn about phishing protection, transaction scanning, and essential security tips to safeguard your crypto assets.

Crypto Wallet Drainers: How to Stay Safe in Web3
Learn how crypto wallet drainers work, recognize attacks, and protect your digital assets. Comprehensive guide with case studies and best practices.
Glossary

Decentralized Application (dApp)
Learn what a decentralized application is, how dApps work on blockchains like Ethereum and Solana, and the security risks every Web3 user needs to watch for.

Liquidity
Learn what liquidity means in crypto, how liquidity pools power DeFi trading, and the security risks of providing liquidity in Web3.

Proof of Stake (PoS)
Learn what Proof of Stake is, how PoS validators secure blockchains like Ethereum and Solana, and the security risks users should know about.

Proof of Work (PoW)
Learn what Proof of Work is, how PoW mining secures blockchains like Bitcoin, and the security trade-offs every crypto user should understand.

Yield Farming
Learn what yield farming is, how it generates returns in DeFi, and the security risks every crypto user should understand before chasing high APYs.
AMM (Automated Market Maker)
Learn what Automated Market Makers are, how they enable DeFi trading, and the security risks you need to know.

Blockchain
Learn what a blockchain is, how it works as a distributed ledger, and why its immutability makes it both powerful and a target for scammers.

Cryptocurrency
Learn what cryptocurrency is, how it works as digital money on a blockchain, and the key security risks every crypto user needs to know about.
Centralized Exchange (CEX)
Learn what a centralized exchange (CEX) is, how it differs from a DEX, and the key security risks of storing crypto on exchange platforms.

Gas Fee
Learn what a gas fee is in crypto, how it's calculated on Ethereum and other blockchains, and how bots exploit gas to extract value from everyday traders.

Impersonation Attack
Learn what impersonation attacks are, how scammers exploit trust, and how to verify identities in Web3.

Layer-1
Learn what a Layer-1 blockchain is, how it differs from Layer-2 networks, and why its security architecture is the foundation everything in crypto is built on.

Layer 2
Learn what a Layer-2 network is, how rollups and state channels work, and what security risks exist when moving assets between Layer-1 and Layer-2 blockchains.
Liquidity Pool Drain
Learn what liquidity pool drains are, how hackers exploit DeFi protocols, and how to protect your funds.

Oracle Manipulation
Learn what oracle manipulation is, how attackers exploit price feeds, and why it threatens DeFi protocols.
Public Key
Learn about Public Key in our Web3 security glossary.

Seed Phrase
Learn what a seed phrase is, how it controls access to your crypto wallet, and why losing or exposing it can result in permanent, unrecoverable loss.
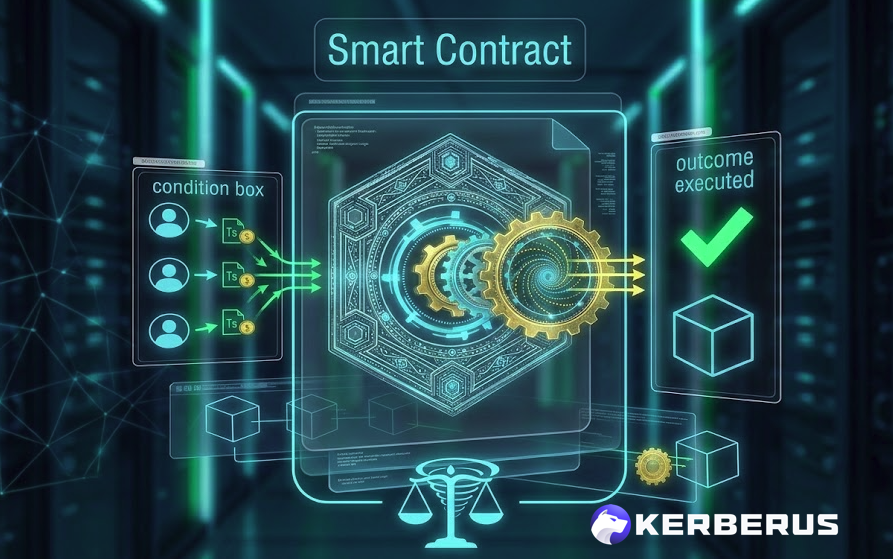
Smart Contract
Learn what a smart contract is, how it self-executes on a blockchain, and why smart contract vulnerabilities are one of crypto's biggest security risks.

Token
Learn what a crypto token is, how tokens differ from coins, and the security risks of interacting with unknown or unverified tokens.

$5 Wrench Attack
Learn what wrench attacks are, how physical coercion threatens crypto holders, and essential personal security measures.

AI Crypto Scam
An AI crypto scam uses artificial intelligence to create sophisticated cryptocurrency fraud including deepfakes, cloned voices, and personalized phishing.
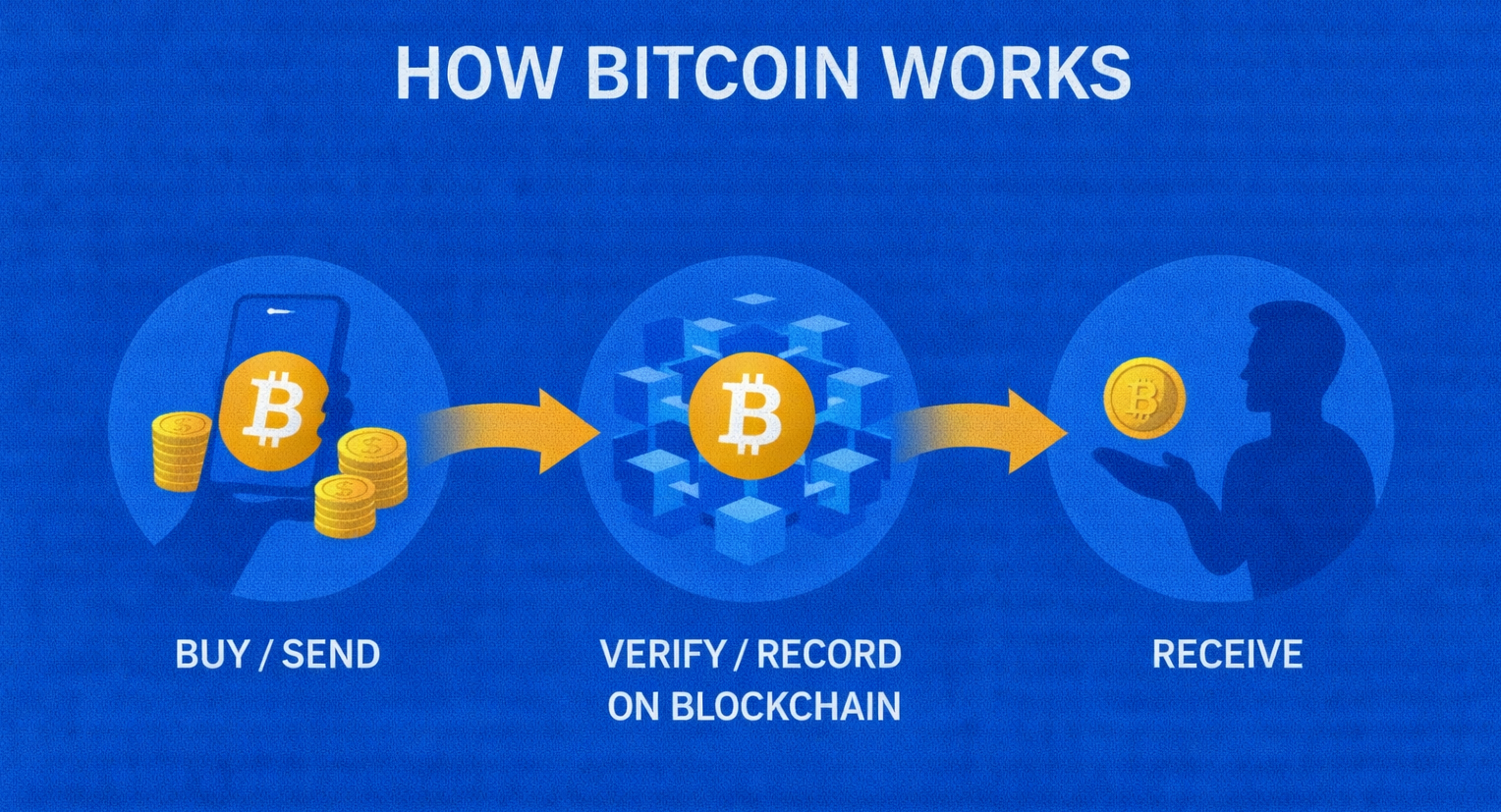
Bitcoin
Bitcoin is the world's first decentralized digital currency, created in 2009 by Satoshi Nakamoto enabling peer-to-peer transactions without intermediaries.
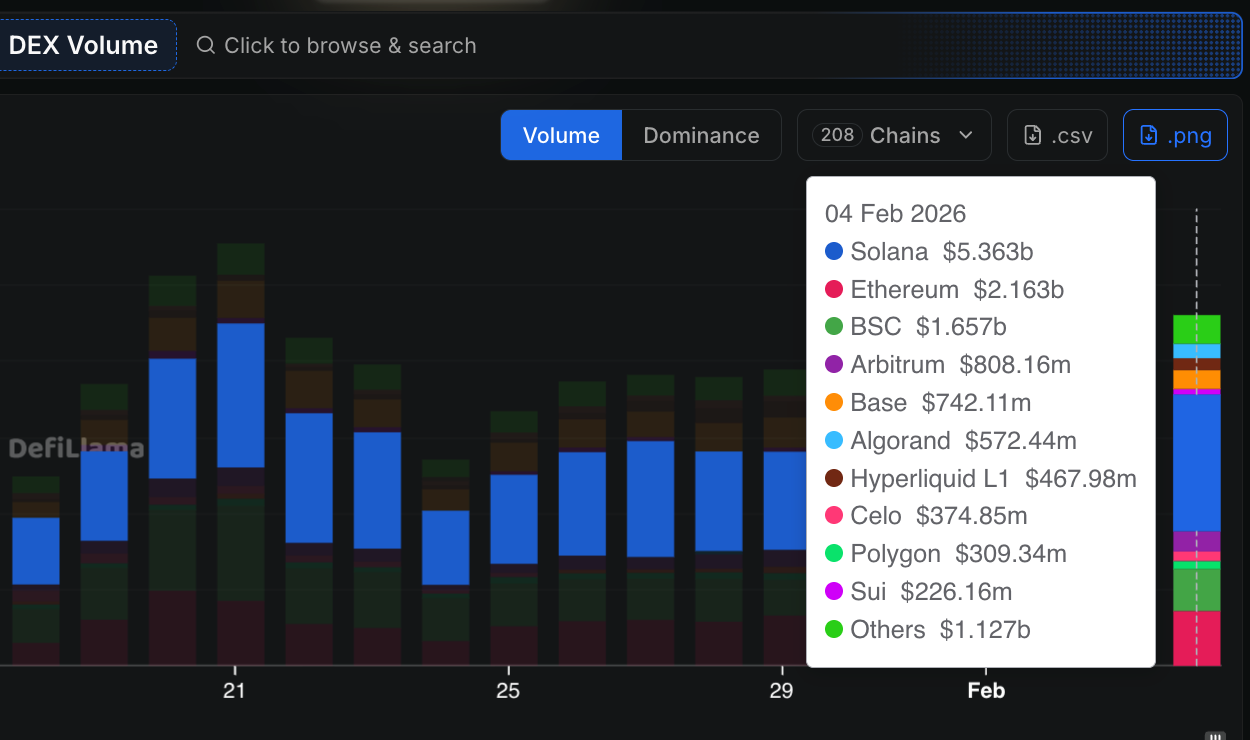
Decentralized Exchange (DEX)
A DEX is a cryptocurrency trading platform that operates through smart contracts, allowing users to trade without centralized intermediaries.
DeFi (Decentralized Finance)
DeFi is a blockchain-based financial ecosystem that recreates traditional banking through smart contracts without intermediaries.

Ethereum Virtual Machine (EVM)
The EVM is a decentralized computing environment that executes smart contracts on the Ethereum blockchain.
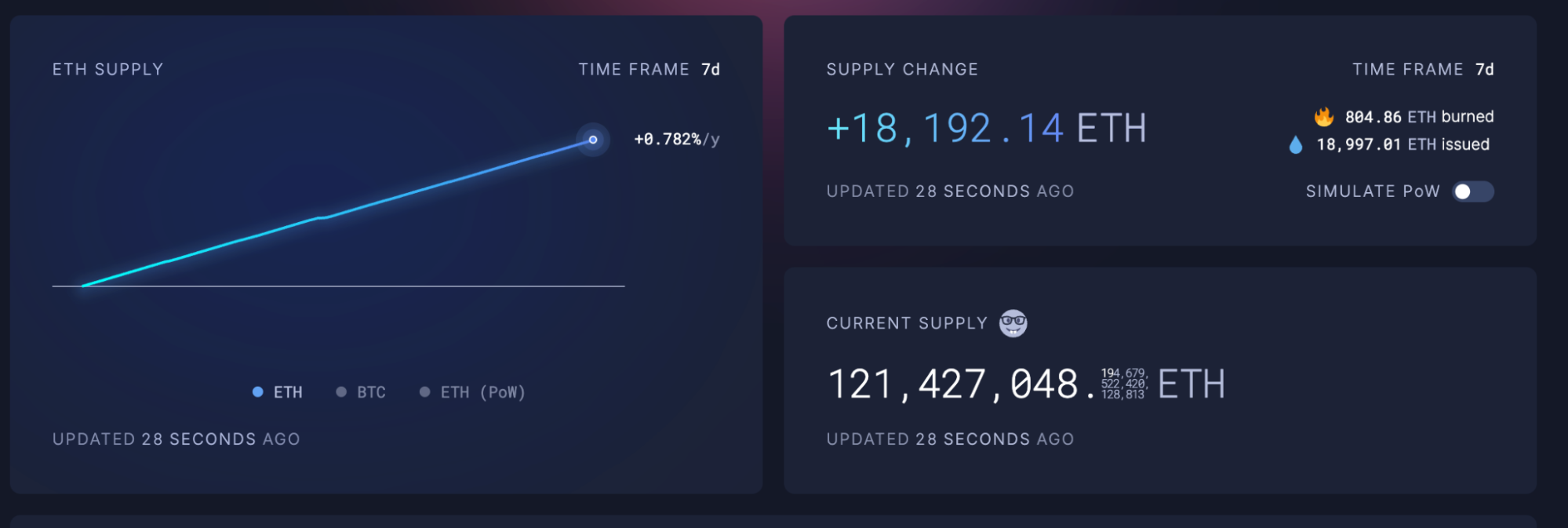
Ethereum
Ethereum is a decentralized blockchain platform that enables smart contracts and dApps through its programmable virtual machine.
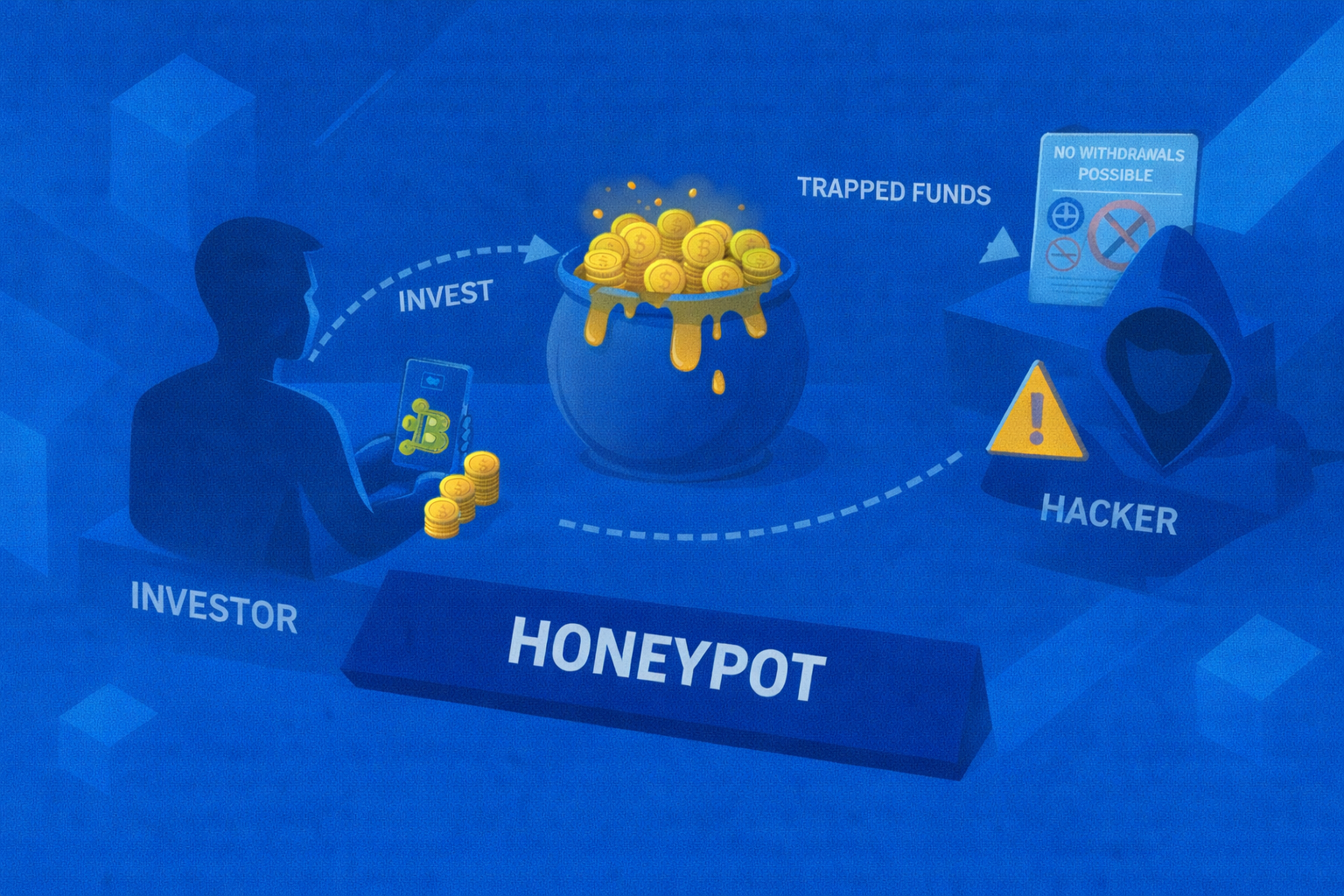
Honeypot
Learn what a honeypot smart contract is and how these crypto traps work to steal funds.
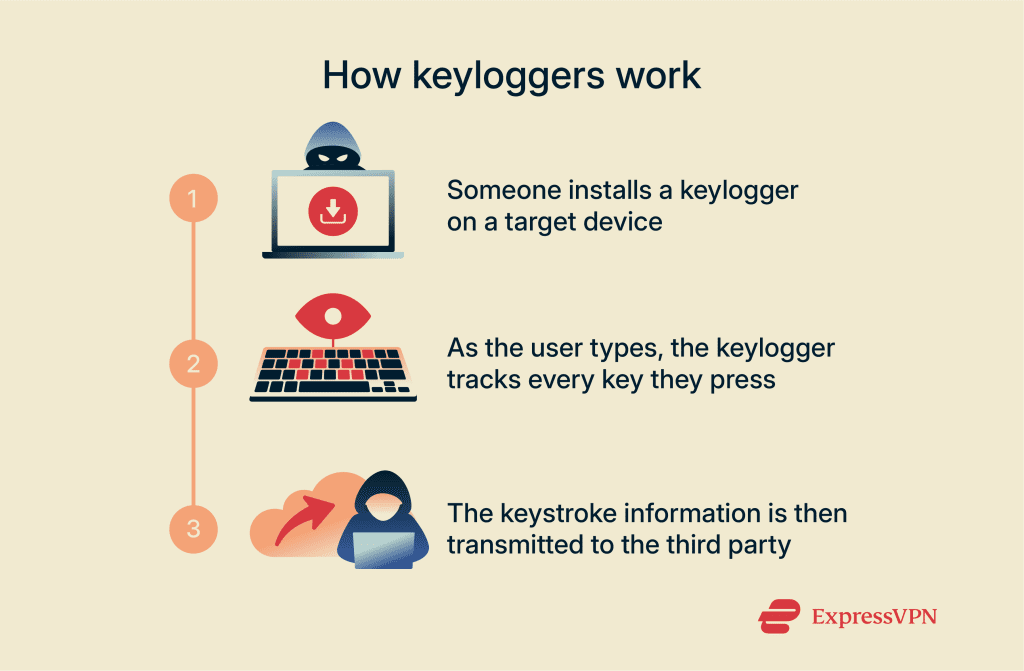
Keylogger
A keylogger is malicious software or hardware that secretly records keystrokes to capture private keys, seed phrases, and passwords.
Malware
Malware is malicious software designed to infiltrate devices, steal data, or gain unauthorized control. In crypto, malware often targets private keys and wallets.

MEV Attack
Learn what an MEV attack is, how it works, and how users can reduce risk in Web3.

Non-Custodial Wallet
A non-custodial wallet gives users complete control over private keys and funds without third-party custody.
Quantum Computing
Quantum computing leverages quantum mechanical phenomena to process information exponentially faster than classical computers for certain problems.
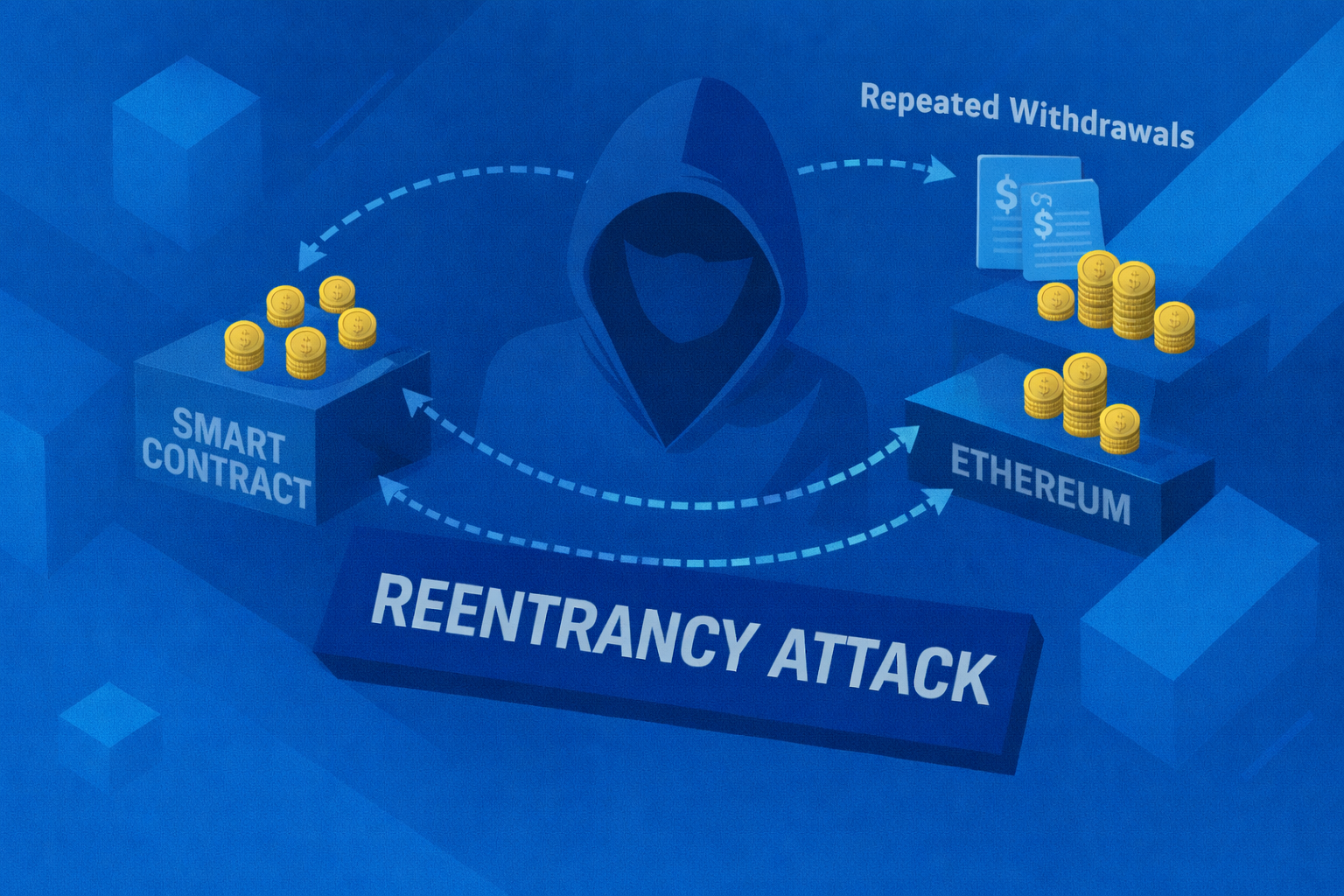
Reentrancy Attack
Learn what a reentrancy attack is and why it remains a critical smart contract risk.

Sybil Attack
A Sybil attack is when a single entity creates multiple fake identities to gain disproportionate influence over a decentralized network.

Solana
Solana is a Top 10 ranked high-performance layer-1 blockchain designed for fast, low-cost transactions using Proof of Stake and Proof of History.

Web3
Web3 is the decentralized internet owned by users. Learn how blockchain, crypto, and dApps work, and the security challenges you face.

Web3 Wallet
A Web3 wallet stores your private keys and crypto. Learn how wallets work, different types, and how to secure them against hackers.

Social Engineering
Social engineering attacks manipulate you into revealing secrets. Learn to spot psychological tricks and protect your crypto assets.

Web3 Security
Web3 security protects you from hacks and scams. Learn about wallet security, smart contract risks, and how to stay safe in crypto.

Phishing
Web3 phishing attacks impersonate trusted sites to steal your keys. Learn to spot fake websites and protect your wallet with Kerberus.
Transaction Poisoning
Transaction poisoning tricks you into copying fake addresses. Learn how this scam works and how to verify recipients with Kerberus.

Smart Contract Vulnerability
Smart contract bugs can cause massive crypto losses. Learn about common vulnerabilities and how to check contracts before investing.

ApprovalForAll Exploit
The setApprovalForAll exploit lets scammers steal all your NFTs. Learn how this attack works and how to manage permissions safely.

Rugpull
Rugpulls happen when developers steal investor funds. Learn to spot exit scams and protect your investments with our guide.

Private Key
Your private key controls your crypto. Learn how it works, why it's crucial for security, and how to keep it safe from theft.

Non-Fungible Tokens (NFT)
NFTs are unique digital assets on the blockchain. Learn how NFTs work, their use cases, and how to protect your collection from theft.

Multisig Wallet
Multisig wallets require multiple keys for transactions, offering better security. Learn how they work and when to use them for your crypto assets.

Malicious Approvals
Malicious approvals let scammers drain your wallet. Learn to spot dangerous permissions and revoke them to secure your crypto.

Front-End Compromise
Attackers hack dApp front-ends to steal your crypto. Learn how front-end compromises happen and how to verify websites with Kerberus.

Flash-Loan Attack
Flash-loan attacks exploit DeFi protocols for risk-free profit. Learn how these complex attacks work and how to protect your assets.

Fake Airdrop Scam
Fake airdrops promise free tokens to steal your crypto. Learn to spot scam campaigns and protect your wallet from malicious claims.

DaaS (Drainer-as-a-Service)
Drainer-as-a-Service (DaaS) platforms empower criminals to steal crypto. Understand the threat and protect your wallet from organized scams.

Crypto Wallet Drainer
Wallet drainers steal crypto by tricking you into approving transactions. Learn how they work and how to block them with Kerberus.

Cross-Chain Bridge Vulnerability
Cross-chain bridge hacks cause massive crypto losses. Learn how bridge exploits work and how to protect your assets when moving funds.
Address Poisoning
Address poisoning attacks trick you into sending crypto to scammers. Learn how to spot fake addresses and secure your wallet with Kerberus.