Liquidity Pool Drain
Learn what liquidity pool drains are, how hackers exploit DeFi protocols, and how to protect your funds.
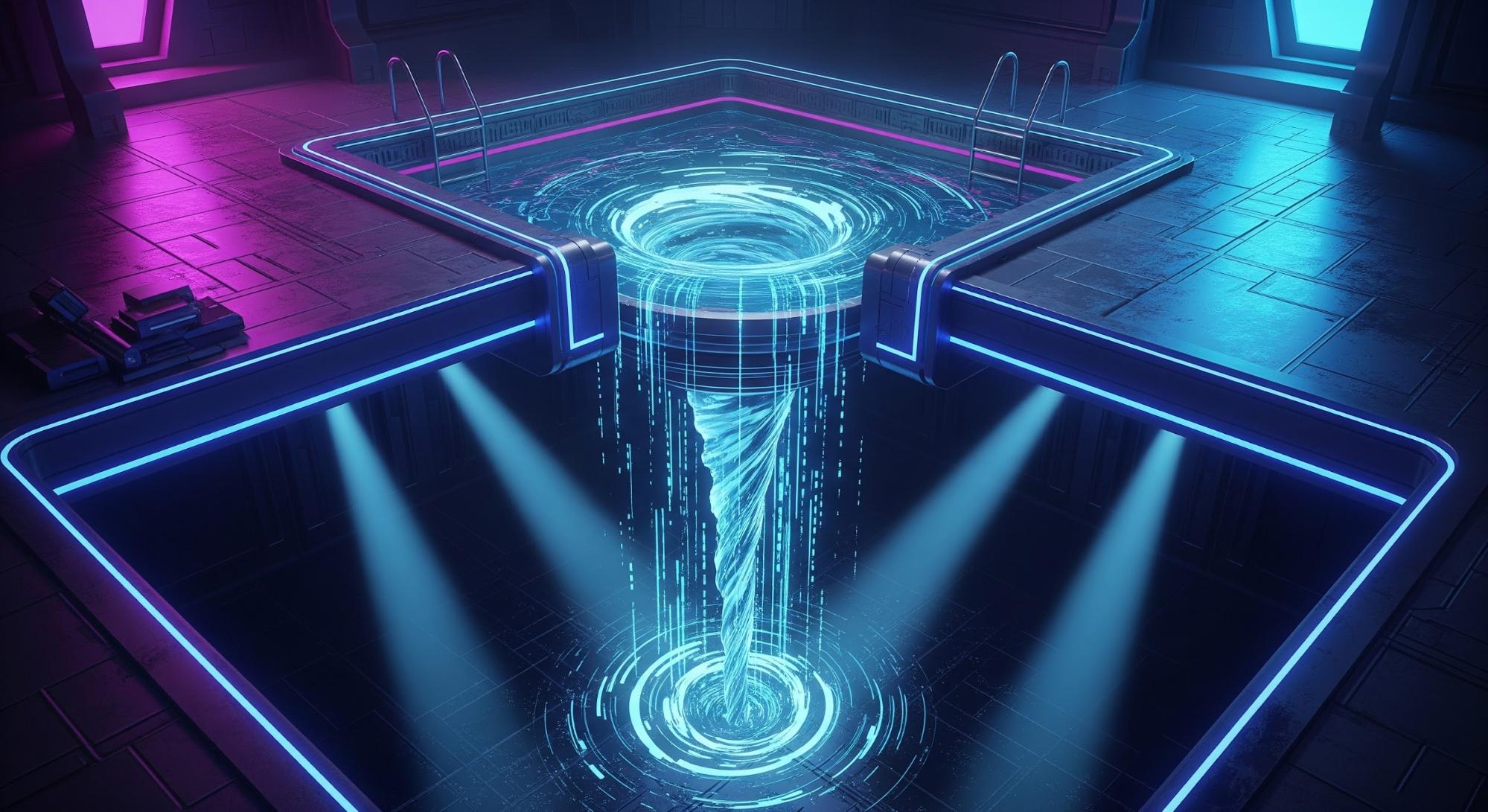
What Is a Liquidity Pool Drain?
A liquidity pool drain happens when hackers find and exploit weaknesses in a DeFi protocol to steal most or all of the funds that users have deposited. It can be equated to finding a hidden backdoor in a bank vault and walking out with everyone’s money.
How It Works
These attacks usually exploit mistakes in how a protocol calculates prices, manages permissions, or handles interactions between different smart contracts. Hackers might manipulate token prices, trick the system into releasing funds multiple times, or combine several attack methods at once. Because everything happens automatically through code, attackers can drain millions of dollars in seconds, sometimes completing the entire theft in a single transaction.
Here’s a typical scenario: an attacker spots a flaw in how a pool values tokens. They borrow a huge amount of crypto (using something called a flash loan), execute trades that confuse the system’s pricing, drain the pool, repay their loan, and vanish, all before anyone notices what happened. It’s like a bank heist that happens faster than you can blink.
Why It Matters
Liquidity pool drains can destroy entire platforms overnight and often look like exit scams, even when they’re actually technical exploits. In October 2024, Radiant Capital lost over $50 million when attackers exploited how different parts of their system interacted. The hack showed how one weak link can bring down an entire protocol.
Throughout 2024, dozens of smaller DeFi platforms lost millions to similar attacks. Some shut down permanently, leaving users with nothing. These incidents remind us that in DeFi, your funds are only as secure as the code protecting them.
-
Stick to well-established platforms with security audits and proven track records
-
Never put all your funds in one protocol, spread them across multiple platforms
-
Understanding smart contract vulnerabilities is crucial
-
If a yield opportunity seems too good to be true, it probably is
-
Use Web3 security tools like Kerberus and Pocket Universe to get real-time protection and warnings when interacting with Web3 platforms
-
Check our Learn academy for top crypto safety information
Written by:
Werner Vermaak is a Web3 author and crypto journalist with a strong interest in cybersecurity, DeFi, and emerging blockchain infrastructure. With more than eight years of industry experience creating over 1000 educational articles for leading Web3 teams, he produces clear, accurate, and actionable organic material for crypto users.
- •8+ years in crypto & blockchain journalism
- •1000+ educational articles for leading Web3 teams
- •Former content lead at CoinMarketCap, Bybit, OKX
Related Terms
See more glossary termsInstall once & immediately get protected from scams, phishing and hacks. Zero losses for 250k+ users in 3 years. Now with up to $30,000 in coverage.




